Synametrics Technologies
Revolving around the core of technology
Document information
| Document ID: | 2181 |
|---|---|
| Subject: | Privacy concerns when sharing files on the cloud/Internet |
| Creation date: | 9/21/12 5:02 PM |
| Last modified on: | 12/18/20 12:06 PM |
Privacy concerns when sharing files on the Internet
The amount of internet users sharing their private data through third-party file sharing is rapidly increasing. Some even use these services to backup their data in the cloud. Although these services are very easy to setup and are available at a very low price, the cost of privacy may be too high for some to afford and it is very important to understand this cost before using these services.Online file sharing and backup services
To fully understand the problem, you need to explore how these services work.When you sign up for any service, you supply a user name and password then install the application. As long as you're connected to the Internet, the files you drag into the local folder magically appear on all PCs, laptops, and mobile devices that also have that service installed and are attached to the same account. Some services also allow you to access your files using a browser from any machine.
Additionally, some companies may obtain private information like:
- Your name
- Address
- Credit card
- Number of computers you have and their type
Blackbox Approach
Almost every online backup or file sharing service provider employ a blackbox approach. This means clients never have to worry about:- How files get to the other end
- How are files stored
- Where are the servers physically located
- Which encryption mechanism, if any, they use
- Who has access to those files
- Are backups of your data being made, and how secure are those back environments
Problem Statement
Due to the blackbox approach specified above, it is almost impossible to guarantee the privacy of your data. Although most companies claim they use encryption to protect data, there can always be leaks or bugs in their software that can make your private data vulnerable to hackers.Consider a scenario where a service provider allows you to search or modify documents on their server. There is no way to either search or modify any document unless that document is in clear (not encrypted). Assuming the document is encrypted; the software used to provide this service has to be able to decrypt it, allow you to modify and finally, encrypt it again before storing it to the disk. A small glitch in the software performing this task can make your files available to any hacker. Moreover, there is a very good chance developers of this technology can access your document while debugging the application.
Additionally, there is no way for a company to use deduplication if files are encrypted with different keys. This is because a file encrypted with two different keys will generate a completely different output and deduplication cannot be used.
It is common knowledge that financial, insurance and government institutions have secure networks and stringent rules on how to protect consumer data. One reason why their networks are relatively secure is because of laws that govern these industries, such as Sarbanes-Oxley. Unfortunately, no such law exists for companies that offer online file sharing or backup services, leaving consumers to trust them with their data. Even if the companies keep their word and say the data that is stored is secure, attacks from outside can still happen and cause a problem where confidential data gets leaked. Large companies that have many customer's data are not immune to this.
Here are some examples of data breaches that occurred:
- In August of 2013, according to an article from CNN , Yahoo had a breach attack where hackers stole user's data from around 3 billion accounts. The accounts included names, email addresses and passwords. Yahoo informed their users to change their passwords to prevent their accounts from being accessed.
- Another major breach occurred with eBay. Csoonline published an article which stated that between February and March 2014 a database containing users' information was compromised. Attackers managed to get credentials that belonged to an employee of eBay. This gave the hackers access to eBay's network and user's data such as customers' names, encrypted passwords, email and physical addresses, phone numbers and date of birth.
- In July 2017, Equifax, one of the largest credit bureaus in the U.S. suffered a severe data breach. The data breached occurred due to a vulnerability on one of their applications. According to csoonline, around 143 million user's data was exposed. Information such as Social Security Numbers, addresses, and date of birth was breached. Unfortunately, around 209,000 credit cards had been exposed as well. In response, Equifax has launched a website for the victims that were affected and will offer credit monitoring to all the U.S. customers.
Solution
The best way to protect your data is to prevent it from ever leaving your network and only allow individuals who are authorized. In short, you create a private cloud containing the networks that belong to you. For example, if you have 3 offices designate one of them as a central repository. Users should be able to access their files from these repositories rather than accessing them from a third party company on the Internet.Synametrics Technologies offer two products that allow you to share files and back them up in a secure manner. Both SynaMan and Syncrify are products, not services. This means you install them inside your network and allow access to individuals who need them.
Consider a scenario where you have multiple offices in different physical locations. You can use Syncrify to backup files from different offices to a central location. Additionally, you can use SynaMan to share files with clients and other business partners. The following image depicts a typical network diagram where Syncrify and/or SynaMan is installed.
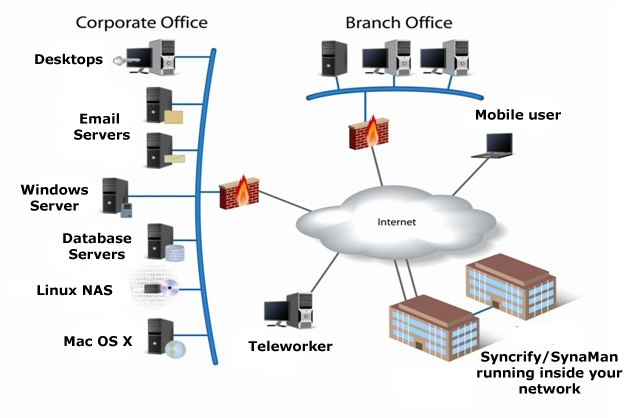
Whether or not you use these products over the Internet or within a LAN, files always stay under your control. In cases where you backup files from one office to another over the Internet, you can use SSL to encrypt the data transmission. Both Syncrify and SynaMan can also work over a VPN connection for added security.
Summary
If privacy is important to you, using an online service for file transfer or backup may turn out to be very costly. The best way to protect your important files from unauthorized access is to keep them within your network.Add a comment to this document
Do you have a helpful tip related to this document that you'd like to share with other users?
Important: This area is reserved for useful tips. Therefore, do not post any questions here. Instead, use our public forums to post questions.
