Synametrics Technologies
Revolving around the core of technology

Since 2017 the United States government requires any federal contractors working with the Department of Defense (DoD) to comply with the standards outlined in NIST 800-171. The document outlines strict rules regarding the handling of sensitive, non-classified, information. NIST 800-171 is quite broad in scope, and applies to many industries and fields, however, it has also been adopted as standard by many state and federal agencies.
The purpose of this document is to outline the requirements of NIST 800-171, as they pertain to SynaMan, and how SynaMan can be used in an environment that requires NIST 800-171 compliance.
SynaMan is a highly scalable private-cloud file sharing and management solution. It offers a multitude of tools to control, manage, share, and secure user data and files, such as:
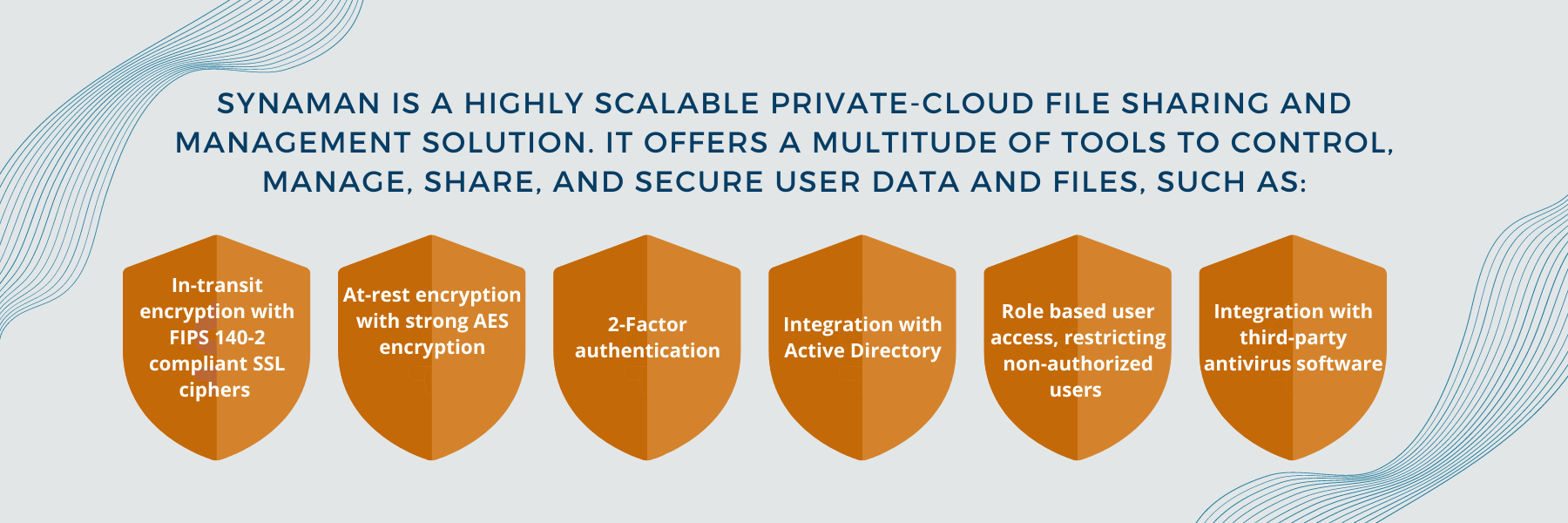
In short, SynaMan provides every tool necessary for you to run a secure file sharing solution that runs inside your company�s network. Your secure files will never be shared by any third-party unless they are authorized.
Since SynaMan is a 100% private, on-premise solution, administrators will have to meet several requirements outlined by NIST in order to stay compliant. Most of these recommendations pertain to the physical environment where the SynaMan server runs. Following table lists all the requirements mentioned within this government document and how SynaMan can assist you in meeting them.
This document is intended to provide an overview and is not intended to provide legal advice. For more comprehensive information on regulation and their implications, please consult your legal counsel.
Click on a button below to be taken to the corresponding NIST requirements:
| Access Control | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.1.1 | Limit information system access to authorized users, processes acting on behalf of authorized users, and devices (including other systems). | SynaMan provides multiple access controls and device management capabilities to comprehensively manage and access the CUI. |
| 3.1.2 | Limit information system access to the types of transactions and functions that authorized users are permitted to execute | SynaMan has access controls that administrators can use to restrict access permissions, including upload and download as well as read and write access controls. |
| 3.1.3 | Control the flow of CUI in accordance with approved authorizations. | "SynaMan contains many useful tools for controlling and monitoring workflow, such as user and administrator groups as well as policy management capabilities that separate duties of individuals accessing SynaMan. SynaMan also provides comprehensive audit logging that captures any activity from both users and administrators. |
| 3.1.4 | Separate the duties of individuals to reduce the risk of malevolent activity without collusion. | SynaMan offers two types of roles, Administrators and non-admin users. Non-admin users can only share files with other users. They cannot perform any administrative tasks. Additionally, any interactions with the SynaMan console are thoroughly logged for easy audit access. |
| 3.1.5 | Employ the principle of least privilege, including for specific security functions and privileged accounts. | SynaMan's policy-based access management system allows system administrators to define access policies for both administrators and users that employ the principle of least privilege. |
| 3.1.6 | Use non-privileged accounts or roles when accessing non-security functions. | SynaMan offers role-bassed access controls to access non-security functions. |
| 3.1.7 | Prevent non-privileged users from executing privileged functions and audit the execution of such functions. | SynaMan prevents non-privileged users from performing administrator duties. Any actions that are performed by both administrators and users are kept in detailed audit logs. |
| 3.1.8 | Limit unsuccessful logon attempts | SynaMan has the ability for administrators to set a number of incorrect login attempts made and will block the IP address once the threshold is reached. |
| 3.1.9 | Provide privacy and security notices consistent with applicable CUI rules. | SynaMan is a private-cloud product. Customers can create their own privacy, Terms of Service, and security policies. |
| 3.1.10 | Use session lock with patternhiding displays to prevent access and viewing of data after period of inactivity. | SynaMan contains session-locking pre-configured. After a set period of time, user sessions are terminated. |
| 3.1.11 | Terminate (automatically) a user session after a defined condition. | SynaMan contains a configurable session-timeout setting that will automatically log users and administrators out once the time has been reached. The user and administrator must log in again to regain access. |
| 3.1.12 | Monitor and control remote access sessions. | SynaMan's audit and control capabilities modify every action taken by both administrators and users within the system. Administrators can easily monitor the audit logs and control user access if needed. |
| 3.1.13 | Employ cryptographic mechanisms to protect the confidentiality of remote access sessions. | SynaMan protects the confidentiality and integrity of your files in transit and at rest. SSL/TLS secure tunnel for files in transmission. |
| 3.1.14 | Route remote access via managed access control points. | SynaMan allows administrators to control which ports are allowed for remote access. System administrators can also choose to deploy additional routing elements, such as a reverse proxy server, on the machine or network SynaMan is installed on. |
| 3.1.15 | Authorize remote execution of privileged commands and remote access to security-relevant information. | SynaMan does not allow remote execution of any privilged commands to non-admin users. Access to administrators can be restricted to localhost. It can also be restricted by IP addresss. |
| 3.1.16 | Authorize wireless access prior to allowing such connections. | SynaMan does not offer any direct wireless access. All access must be done through HTTPS. |
| 3.1.17 | Protect wireless access using authentication and encryption. | SynaMan does not offer any direct wireless access. All access must be done through HTTPS. |
| 3.1.18 | Control connection of mobile devices | Mobile devices connect the same way non-mobile devices connect, through the web browser. SynaMan can blacklist IP addresses, including mobile devices if necessary, as well as utilize network services to ensure only allowed devices can connect. |
| 3.1.19 | Encrypt CUI on mobile devices and mobile computing platforms. | SynaMan is only installed on a single machine, never on a mobile device. |
| 3.1.20 | Verify and control/limit connections to and use of external systems. | Connections to external systems are fully configurable and it is up to the administrators to decide how to limit them. |
| 3.1.21 | Limit use of organizational portable storage devices on external systems. | N/A |
| 3.1.22 | Control CUI posted or processed on publicly accessible systems | SynaMan can only be installed on a single machine. System Administrators can control access to the SynaMan machine at the network layer. |
| Awareness and Training | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.2.1 | Ensure that managers, systems administrators, and users of organizational information systems are made aware of the security risks associated with their activities and of the applicable policies, standards, and procedures related to the security of organizational information systems. | Although training and awareness is the responsibility of the organization deploying SynaMan, we publishes best practices articles on our website that could help while training employees |
| 3.2.2 | Ensure that organizational personnel are adequately trained to carry out their assigned information security-related duties and responsibilities. | N/A - refer to knowledge base articles on our site for tips |
| 3.2.3 | Provide security awareness training on recognizing and reporting potential indicators of insider threat. | N/A - refer to knowledge base articles on our site for tips |
| Audit and Accountability | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.3.1 | Create, protect, and retain information system audit records to the extent needed to enable the monitoring, analysis, investigation, and reporting of unlawful, unauthorized, or inappropriate information system activity. | SynaMan provides comprehensive audit logging (what, when, who, where and how) details. Administrators can export or archive the audit logs for safe keeping. |
| 3.3.2 | Ensure that the actions of individual information system users can be uniquely traced to those users so they can be held accountable for their actions | By providing options to record any action done by any user or administrator, SynaMan gives customers all audit data to satisfy any type of compliance. |
| 3.3.3 | Review and update audited events. | The SynaMan platform helps system administrators and personnel with privileged access to view the audited events. |
| 3.3.4 | Alert in the event of an audit process failure. | SynaMan Audit logs clearly show the audit timeline. Administrators can check it periodically to make sure actions are audited properly. |
| 3.3.5 | Correlate audit review, analysis, and reporting processes for investigation and response to indications of inappropriate, suspicious, or unusual activity. | SynaMan Audit logs can be exported to Security Information and Event Management systems to analyze and identify suspicious or unusual activity. |
| 3.3.6 | Provide audit reduction and report generation to support on-demand analysis and reporting. | SynaMan offers builtin and configurable reports for specified events, as well as a dashboard and audit logging feature that allows for administrators to easily view what files are being handled. |
| 3.3.7 | Provide an information system capability that compares and synchronizes internal system clocks with an authoritative source to generate time stamps for audit records. | All SynaMan logs and audit records contain machine-synchronized time-stamps. Therefore, it is important to ensure the machine's clock is synchronized with an NTP server. |
| 3.3.8 | Protect audit information and audit tools from unauthorized access, modification, and deletion. | Audit information is stored on the machine SynaMan is installed on. System Administrators can use a variety of tools of their choice to secure and maintain this data. It is important for organizations to ensure unauthorized users cannot get access to the machine where SynaMan is running. |
| 3.3.9 | Limit management of audit functionality to a subset of privileged users. | Only privileged users of SynaMan and the machine where SynaMan is installed have the ability to manage or access audit functionality. |
| Configuration Management | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.4.1 | Establish and maintain baseline configurations and inventories of organizational information systems (including hardware, software, firmware, and documentation) throughout the respective system development life cycles. | SynaMan provides information via the administrator portal regarding disk and system configurations. |
| 3.4.2 | Establish and enforce security configuration settings for information technology products employed in organizational information systems. | The SynaMan Admin Console provides security settings for the platform that can be easily configured by the system administrators. |
| 3.4.3 | Track, review, approve/disapprove, and audit changes to information systems | SynaMan records administrator actions in the audit log. |
| 3.4.4 | Analyze the security impact of changes prior to implementation. | SynaMan offers enterprise security practices documentation. SynaMan administrators can configure the system as per the guidelines to run the system securely. |
| 3.4.5 | Define, document, approve, and enforce physical and logical access restrictions associated with changes to the information system. | SynaMan enforces logical access as defined by the system administrators. SynaMan audit logs track all logical access. |
| 3.4.6 | Employ the principle of least functionality by configuring the information system to provide only essential capabilities. | SynaMan can be configured to provide the least and essential access to te CUI data. |
| 3.4.7 | Restrict, disable, and prevent the use of nonessential functions, ports, protocols, and services. | SynaMan can be configured to run on a secure port. Administrators can allow only the necessary functions for end-users. |
| 3.4.8 | Apply deny-by-exception (blacklist) policy to prevent the use of unauthorized software or deny-all, permit-by-exception (whitelisting) policy to allow the execution of authorized software. | Users, admin as well as non-admin users can be restricted based on their IP address |
| 3.4.9 | Control and monitor user installed software. | SynaMan prevents unauthorized software from accessing the CUI. Only through the SynaMan explorer can authorized users access the data. |
| Identification and Authentication | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.5.1 | Identify information system users, processes acting on behalf of users, or devices. | SynaMan tracks users and devices activity on the platform using IP addresses and usernames. |
| 3.5.2 | Authenticate (or verify) the identities of those users, processes, or devices, as a prerequisite to allowing access to organizational information systems. | SynaMan offers advanced policy options to enable authentication for users as well as devices before allowing access to organizational information systems. |
| 3.5.3 | Use multifactor authentication for local and network access to privileged accounts and for network access to non-privileged accounts. | SynaMan supports 2FA for users and administrators local and network access |
| 3.5.4 | Employ replay-resistant authentication mechanisms for network access to privileged and nonprivileged accounts. | SynaMan blocks IP addresses if incorrect login credentials are entered a specified number of times . The number can be configured to meet your organization's security requirements. |
| 3.5.5 | Prevent reuse of identifiers for a defined period. | SynaMan prohibits duplicate identifiers within the system. |
| 3.5.6 | Disable identifiers after a defined period of inactivity. | SynaMan allows disabling of user accounts after a specified time period of user inactivity |
| 3.5.7 | Enforce a minimum password complexity and change of characters when new passwords are created. | SynaMan supports strong password policy. The policy requirements can be configured by a system administrator. |
| 3.5.8 | Prohibit password reuse for a specified number of generations. | SynaMan can be integrated with Active Directory to prohibit password reuse. |
| 3.5.9 | Allow temporary password use for system logons with an immediate change to a permanent password. | SynaMan provides an option that will force the new user, on login, to change the password. |
| 3.5.10 | Store and transmit only encrypted representation of passwords. | All passwords are stored and transmitted only in encrypted format. |
| 3.5.11 | Obscure feedback of authentication information. | No other information, besides "password is incorrect" is displayed. |
| Incident Response | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.6.1 | Establish an operational incident handling capability for organizational information systems that includes adequate preparation, detection, analysis, containment, recovery, and user response activities. | N/A |
| 3.6.2 | Track, document, and report incidents to appropriate organizational officials and/or authorities. | The SynaMan platform logs any incidents that administrators can use to document as they wish. |
| 3.6.3 | Test the organizational incident response capability. | N/A |
| Maintenance | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.7.1 | Perform maintenance on organizational information systems. | N/A |
| 3.7.2 | Provide effective controls on the tools, techniques, mechanisms, and personnel used to conduct system maintenance. | System maintenance, such as OS upgrades, is out of scope. However, SynaMan is capable of patching itself to a newer build from the web interface. |
| 3.7.3 | Ensure equipment removed for off-site maintenance is sanitized of any CUI. | SynaMan is only installed on one machine, a central server. User accounts can be removed and data can be cleansed from the server if necessary. |
| 3.7.4 | Check media containing diagnostic and test programs for malicious code before the media are used in the information system. | N/A |
| 3.7.5 | Require multifactor authentication to establish nonlocal maintenance sessions via external network connections and terminate such connections when nonlocal maintenance is complete. | N/A |
| 3.7.6 | Supervise the maintenance activities of maintenance personnel without required access authorization. | N/A |
| Media Protection | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.8.1 | Protect (i.e., physically control and securely store) information system media containing CUI, both paper and digital. | N/A |
| 3.8.2 | Limit access to CUI on information system media to authorized users. | SynaMan protects CUI by enforcing proper access controls. |
| 3.8.3 | Sanitize or destroy information system media containing CUI before disposal or release for reuse. | SynaMan allows administrators to destroy CUI on its machine. |
| 3.8.4 | Mark media with necessary CUI markings and distribution limitations. | N/A |
| 3.8.5 | Control access to media containing CUI and maintain accountability for media during transport outside of controlled areas. | SynaMan enforces access controls on all communication attempts regardless of their location. |
| 3.8.6 | Implement cryptographic mechanisms to protect the confidentiality of information stored on digital media during transport outside of controlled areas unless otherwise protected by alternative physical safeguards. | SynaMan can be integrated with FIPS-140 compliant SSL ciphers as well as at-rest encryption based on AES. |
| 3.8.7 | Control the use of removable media on information system components. | N/A |
| 3.8.8 | Prohibit the use of portable storage devices when such devices have no identifiable owner. | N/A |
| 3.8.9 | Protect the confidentiality of backup CUI at storage locations. | N/A |
| Personnel Security | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.9.1 | Screen individuals prior to authorizing access to information systems containing CUI. | N/A |
| 3.9.2 | Ensure that CUI and information systems containing CUI are protected during and after personnel actions such as terminations and transfers. | When employees and contractors are terminated, SynaMan can revoke permissions of the users and block access to CUI. |
| Physical Protection | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.10.1 | Limit physical access to organizational information systems, equipment, and the respective operating environments to authorized individuals. | N/A |
| 3.10.2 | Protect and monitor the physical facility and support infrastructure for those information systems. | N/A |
| 3.10.3 | Escort visitors and monitor visitor activity. | N/A |
| 3.10.4 | Maintain audit logs of physical access. | N/A |
| 3.10.5 | Control and manage physical access devices. | N/A |
| 3.10.6 | Enforce safeguarding measures for CUI at alternate work sites (e.g., telework sites). | N/A |
| Risk Assessment | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.11.1 | Periodically assess the risk to organizational operations (including mission, functions, image, or reputation), organizational assets, and individuals, resulting from the operation of organizational information systems and the associated processing, storage, or transmission of CUI. | N/A |
| 3.11.2 | Scan for vulnerabilities in the information system and applications periodically and when new vulnerabilities affecting the system are identified. | Enterprise Anti-malware and firewalls can be integrated into SynaMan's environment. |
| 3.11.3 | Remediate vulnerabilities in accordance with assessments of risk. | N/A |
| Security Assessment | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.12.1 | Periodically assess the security controls in organizational information systems to determine if the controls are effective in their application. | SynaMan offers administrative dashboard, alerts, and reports to perform security assessments quickly. |
| 3.12.2 | Develop and implement plans of action designed to correct deficiencies and reduce or eliminate vulnerabilities in organizational information systems | N/A |
| 3.12.3 | Monitor information system security controls on an ongoing basis to ensure the continued effectiveness of the controls. | N/A |
| 3.12.4 | Develop, document, and periodically update system security plans that describe system boundaries, system environments of operation, how security requirements are implemented, and the relationships with or connections to other systems. | N/A |
| System and Communications Protection | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.13.1 | Monitor, control, and protect organizational communications (i.e., information transmitted or received by organizational information systems) at the external boundaries and key internal boundaries of the information systems. | SynaMan monitors, controls, and protects organizational communication in transit and at rest via encryption using FIPS 140- 2 validated encryption module. |
| 3.13.2 | Employ architectural designs, software development techniques, and systems engineering principles that promote effective information security within organizational information systems. | N/A |
| 3.13.3 | Separate user functionality from information system management functionality (e.g., privileged user functions). | SynaMan offers an Admin portal which is separate from the end User portal. Further, the Admin portal can be configured with rolebased access control for privileged user functions. |
| 3.13.4 | Prevent unauthorized and unintended information transfer via shared system resources. | SynaMan prevents unauthorized access or sharing of CUI. Only authorized users can share information via SynaMan. SynaMan also has the option to disable public sharing and disabling new user invites in such a way that the information is kept only within the organization and authorized users. |
| 3.13.5 | Implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks. | SynaMan can be deployed with a DMZ allowing network separation. It could also run behind a reverse proxy if needed. |
| 3.13.6 | Deny network communications traffic by default and allow network communications traffic by exception (i.e., deny all, permit by exception). | This can be achieved with a combination of network firewalls as well as a list of IP addresses allowed to connect. |
| 3.13.7 | Prevent remote devices from simultaneously establishing nonremote connections with the information system and communicating via some other connection to resources in external networks. | N/A |
| 3.13.8 | Implement cryptographic mechanisms to prevent unauthorized disclosure of CUI during transmission unless otherwise protected by alternative physical safeguards. | SynaMan encrypts CUI in transit using TLS 1.2 (Transport Layer Security) as well as industry standard options for SSL. |
| 3.13.9 | Terminate network connections associated with communications sessions at the end of the sessions or after a defined period of inactivity. | SynaMan provides session timeout for both the end User and Admin portal that can be configured by the system administrators. After a defined period of inactivity, the user, as well as the admin session, expires. |
| 3.13.10 | Establish and manage cryptographic keys for cryptography employed in the information system. | SynaMan automatically creates random cryptographic keys that are used for encryption. Deleting existing keys will force the system to recreate them. |
| 3.13.11 | Employ FIPS-validated cryptography when used to protect the confidentiality of CUI. | SynaMan can be integrated with FIPS-validated cryptography modules that are approved by NIST. |
| 3.13.12 | Prohibit remote activation of collaborative computing devices and provide indication of devices in use to users present at the device. | N/A |
| 3.13.13 | Control and monitor the use of mobile code. | N/A |
| 3.13.14 | Control and monitor the use of Voice over Internet Protocol (VoIP) technologies. | N/A |
| 3.13.15 | Protect the authenticity of communications sessions. | SynaMan invalidates the session upon user logout or upon a defined period of inactivity. |
| 3.13.16 | Protect the confidentiality of CUI at rest. | At rest encryption is provided using strong-AES encryption. |
| System and Information Integrity | Details | How SynaMan Supports NIST 800-171 Compliance |
|---|---|---|
| 3.14.1 | Identify, report, and correct information and information system flaws in a timely manner. | N/A |
| 3.14.2 | Provide protection from malicious code at appropriate locations within organizational information systems. | SynaMan can be integrated with anti-malware software to scan and prevent viruses, APTs, and zero-day attacks. SynaMan is installed on a single machine and allows administrators to secure the machine according to their organizational security standards. |
| 3.14.3 | Monitor information system security alerts and advisories and take appropriate actions in response. | SynaMan is installed on a single machine and allows system administrators to integrate any security protocols and applications they wish to monitor system integrity and alert administrators. |
| 3.14.4 | Update malicious code protection mechanisms when new releases are available. | SynaMan is installed on a single machine and can be integrated with anti-malware products. These products can be updated regularly as new definitions are released by the vendor. |
| 3.14.5 | Perform periodic scans of the information system and real-time scans of files from external sources as files are downloaded, opened, or executed. | SynaMan is installed on a single machine and can be integrated with anti-malware products. Administrators can utilize these products to perform real-time scans of files. |
| 3.14.6 | Monitor the information system, including inbound and outbound communications traffic, to detect attacks and indicators of potential attacks. | SynaMan can monitor traffic in conjunction with third-party traffic monitoring applications to detect attacks. In addition to this, SynaMan offers a multitude of features such as CSRF protection as well as SSL to ensure communication is secure. |
| 3.14.7 | Identify unauthorized use of the information system. | SynaMan's web portal does not permit unauthorized access to the system. The system itself can be protected by system administrators in any way they see fit. |
Related Articles














