Synametrics Technologies
Revolving around the core of technology
Acer's $50 Million Ransomware Attack And How To Ensure Protection For Your Company Against Ransomware Attackers.
With $50 million dollars on the line, a recent ransomware attack on Acer may encourage other large organizations to take cybersecurity more seriously. Earlier this week, cybercrime group REvil made the highest ransomware demand ever to PC manufacturer Acer. The threat? Provide $50 million of extortion money in cryptocurrency by March 28, or the ask doubles. If Acer fails to comply, the attackers might leak the pilfered files belonging to Acer and its customers. REvil ransomware, the cybercriminal group that attacked the Taiwanese PC manufacturer Acer also launched a ransomware attack on a New York-based law firm in May 2020, demanding $42 million in extortion money in exchange for not releasing sensitive information about their high-profile clients. This same notorious group is responsible for jeopardizing Travelex's online services, rendering them incapable of operating for up two weeks following December 31st, 2019, when the attack was launched. Ransomware attacks are mainly carried out using emails, and in the worst-case scenario, they could pose an existential threat to corporations that fall victim. This might prompt you to ask the following question...
What does this ransomware attack mean for your business?
Acer's episode is certainly encouraging other large organizations to take cybersecurity more seriously. But what about small and medium-sized businesses?Bullguard, a cybersecurity company, published a research study in January 2020, which exposes how vulnerable yet reckless small and medium-sized businesses are about their cybersecurity. Additionally:
Seeing the juxtaposition above, we hope it is clear that small businesses need to stop rolling the dice on their cybersecurity measures and take informed actions to safeguard their businesses from the ever-increasing risk of cyberattacks. And ransomware is the second most common malware attack, with email being the critical mechanism for all forms of malware.
How is a ransomware attack carried out?
Cybercriminals like REvil can easily commandeer private company information in a few simple steps:- Attackers deliver the malware in the form of email.
- The malware informs the cybercriminal that a victim has opened the malware and cryptographic keys are employed to encrypt a victim's data.
- Attackers send the ransom note threatening to manipulate or expose confidential files if the victim does not cooperate.
- Victims either pay the ransom and hope decryption keys are sent, OR the malware infection is manually removed, and data is recovered in a tedious and time-consuming process.
Whether it be phishing links or a questionable attachment, mistakes can easily be made if security is not taken seriously, as seen in Acer's case. A ransom request of this caliber leads experts to believe that the REvil group is holding onto information that can be highly confidential or can be utilized to launch further cyber-attacks on many of Acer's customers. A source from Bleeping Computer notes that the attack published what appears to be stolen files including bank balances, financial spreadsheets, and other financial communications.
With the gigantic threat hanging over the head of a high-profit business, large corporations worldwide are questioning whether Acer's consideration to pay may promote this cruel cyberattacking business model. Other cyber criminals may be enticed to follow in the footsteps of REvil and begin seeking out other large companies to attack. The looming threat of increased attacks should lead all business owners and employees to take charge of security and create a more regimented cyber safety routine to ensure personal and private information is not exploited for a cybercriminal's monetary gain. There are a few simple steps employees can take and policies business owners can enact to ensure data stays secure and communication remains private and uncompromised. Employees must monitor their emails, and ensure they aren't clicking on any questionable links while also ensuring important information is stored and backed up . While this can appear to be a lot for one person to take on, and mistakes can still be made, other outlets ensure greater protection and reduce the risk of malware threats.
What should businesses around the globe do to protect themselves against ransomware attacks?
It starts with the first and most essential step of cybersecurity, i.e., email security. Emails are the first and foremost way for cybercriminals to attack your business. There are a few simple steps employees can take and policies business owners can enact to ensure data stays secure and communication remains private and uncompromised. they are as follows -
- The business owner needs to set up a system to monitor their organization's emails.
- Employees must ensure they aren't clicking on any questionable links.
- All important organization data must be backed up and secured privately.
- Spam emails with suspicious files, URLs, and hidden codes must be prevented from entering your inbox.
The Email Server Solution
Xeams is a single platform that enables users to protect, manage, and report on email traffic flowing in and out of their organization. Including a state-of-the-art SMTP relay and a powerful policy engine, Xeams monitors messages at the Internet gateway with a complete set of email security capabilities to greatly reduce the threat of attack. With sophisticated filtering, monitoring, encryption, and reporting capabilities, this email server can make it easy for business administrators and management to monitor any message coming and going out of your network. Additionally, with the Xeams Junk Filtering feature, 99% of junk messages are blocked from reaching users' inboxes. This ensures that users will not be tempted to click on any questionable links as they will never reach them.
Added Layer of Security for Microsoft Exchange Serevers
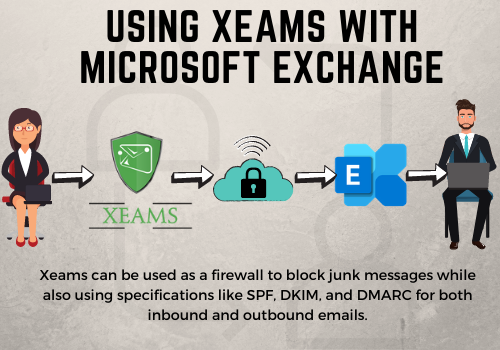
The report from Bleeping Computer also claims that a cyber-intelligence platform detected that REvil targeted a Microsoft Exchange server on Acer's domain. Xeams has the capability to sit in front of a server like Exchange , and be utilized as a firewall to filter messages and ensure only good ones are sent to the actual mail server. Additionally, this will reduce email traffic while preventing any harmful attachments from getting in the way of day-to-day communication. This ensures that users will not be tempted to click on any questionable links, as they will immediately be blocked.
Implementing an email server like Xeams can greatly reduce the risk of ransomware threats to a business. If businesses can learn anything from this threat against Acer, it is that a strong spam fighting solution is key to saving companies millions and avoiding serious data loss. Don't allow your business to get compromised by cybercriminals. Download a free trial of Xeams today and start taking action to prevent ransomware from tearing down your business.
| Created on: | Mar 25, 2021 |
| Last updated on: | Jul 11, 2025 |
