Synametrics Technologies
Revolving around the core of technology
Fake Ransomware is NOT Fake News
You see this message pop-up on your computer screen:
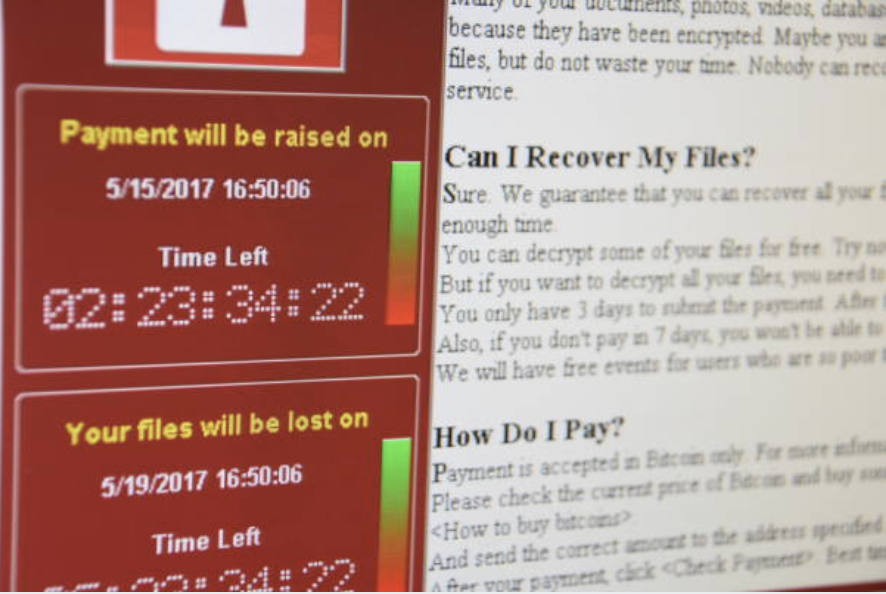
and realize your computer is under the attack of ransomware. All of your important files and documents become encrypted and they only way to access the decryption password is to pay the ransom fee before time runs out.
Ransomware attacks have become growing trend ever since the first ?Trojan Aids? attack in 1989. As we?ve seen over the past couple of years, these attacks have become more wide spread, with hacker groups trying to make as much money as they can.
Imagine being so scared by this tactic that you see a ransomware message pop-up on your screen that you?ll pay for the decryption password before you have the change to determine if the attack is real or fake.
As of lately, a new breed of ransomware has been on the rise, ?Fake? Ransomware. The fake ransomware attacks try to appear as legitimate in order to trick people into paying for a decryption password they wont need, to try and make a profit.
Below we have comprised a list of tips that will help you determine if an attack is real or fake:
- Most ransomware attacks make themselves known by name. Somewhere on the ransom page, the name of the group who created the attack or the specific name of the attack will be made known. Some even go as far as listing a support email you can contact. If you cannot find any information about the ransomware that has attacked your device, it could be an imposter.
- Another thing to keep in mind is encrypted files will be modified. The names of your files may change. Try clicking on your files and if you are able to open them, the ransomware attack is a fake.
- If you are able to close out the ransom using key commands, chances are the attack is fake. Or if you restart your machine and the ransom message disappears, your device is not under attack.
- Check the amount of the ransom. If the attackers are asking for an amount less than $100 the ransom may not be real. In cases of real ransomware attacks the demands is typically above $500.You can also search the web for the payment address or the ransom message and what others are saying about the ransom to determine if the threat is real.
- The hacker groups that put out these ransomware attacks take their time in developing their scheme. They ensure their messages look legitimate and do not contain any spelling errors or grammatical mistakes. If you do see a message that is full of errors its likely an imposter.
- Most importantly, has your network been compromised? Real ransomware attacks typically make their way to your network and spread to other devices. Check your network logs and if nothing seems out of the ordinary, you are in the clear.
In the event of a ransomware attack, a good backup software is key to resorting any compromised files. We recommend Syncrify by Synametrics Technologies. Syncrify is a private cloud backup software that is created within your network. This means backed up files remain in your control and no 3rd party will ever has access to your files. Eliminating the threat of any privacy concerns.
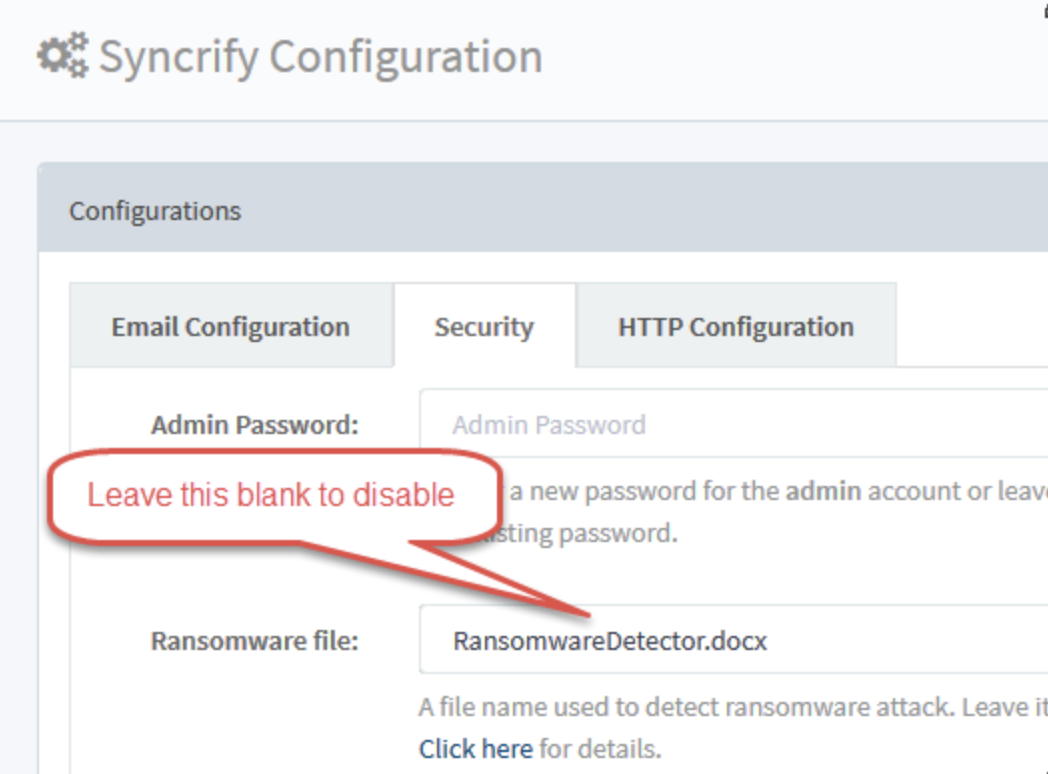
Another great feature of Syncrify is Ransomware Prevention. Through the creation of a ?dummy file? Syncrify can detect if the machine was recently infected with a ransomware virus before a scheduled backup runs. The administrator is alerted via email if such infection is detected and new backups are aborted, saving the previously backed up data.
For more information on ransomware prevention, please visit http://web.synametrics.com/syncrify-ransom-ware.htm. For any additional questions about Syncrify visit http://web.synametrics.com/Syncrify.htm
Or contact our support team via:
Phone: 609-750-0007 option 2
Email: support@synametrics.com
| Created on: | Sep 14, 2018 |
| Last updated on: | Jun 8, 2026 |
